Integration of classic cryptography with QKD
June 18, 2018 – New levels of confidentiality and privacy of communication are strategic features for intelligent transport systems, e-health, transmission of biometric data, e-government, e-commerce and many others services. Introducing Quantum Key Distribution (QKD) in underlying infrastructures has the potential to maintain end-to-end security in the long-term.
Current limitations of QKD are high cost of dedicated hardware, transmission distance limited to few tens of kilometres, and low key transmission rate.
However, for specific applications for which strong security conditions must be met, QKD will likely become an increasingly attractive option in the upcoming years. Now the technology is sufficiently mature to move to practical deployment of EU-wide benefit. The cornerstone of its industrialization is the interoperability of quantum and classical networks, as well as multi-technology, multi-vendor interoperability.
Confidentiality of data and communications, authentication, as well as the long-term privacy and integrity of stored data must be guaranteed for Europe’s digital infrastructures, services and data integrity, supporting European Digital Single Market strategy. Therefore it is strategically important for EU to develop a solution to secure its critical digital infrastructures, like energy, transport, health, finance, etc..
As mentioned in the article Quantum Key Distribution: the new frontier of Security, QKD has provable security. Due to quantum physics, quantum encrypted messages are totally immune from eavesdropping, allowing secure transmission of encryption keys, something that is impossible with classical, non-quantum means. In fact, traditional public key cryptography relies on the computational difficulty of certain mathematical functions and cannot provide any proof of 100% security. Present cryptography will become completely non-secure by more-powerful computer or by the realization of a Quantum Computer, or new mathematical/algorithmical findings.
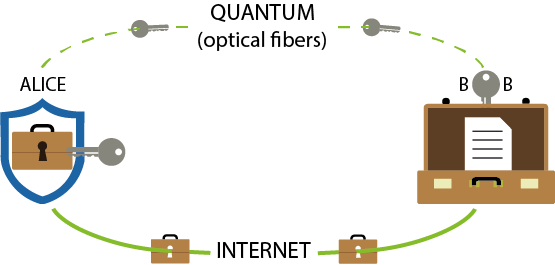
Lively activity and rapid progress of quantum physics applied to Cyber Security during recent years is accelerating the Introduction of QKD in existing infrastructures. On the other hand, in order to make it possible in a short time, it is useless to apply the quantum technologies to all the elements of the cryptography. QKD shall be used only to transmit a key, not any message data. It is important to underline that this key can then be used with any chosen encryption algorithm to encrypt (and decrypt) a message, which will be transmitted over a standard communication channel.
The quantum channel uses optical fiber links to send photons (quantum states of light) between the two parties, whereas the classical channel could be a simple telephone line that the two parties use to talk to each other. Both of these can be public. QKD can be implemented on existing optical infrastructures, but the quantum channel cannot pass through optical amplifiers. While classical signals in the optical infrastructure use repeater nodes throughout the network to amplify and propagate the signal, there are challenges in developing a repeater system for a QKD network. The present solution to this problem is to concatenate multiple QKD systems to let keys propagate via intermediate nodes, which requires them to be trusted to some extent. Routing QKD using trusted nodes is one solution to the distance limitations and point-to-point nature, but it is important that research explores quantum repeater architectures to exploit something known as quantum entanglement in order to extend the range of QKD links beyond 20-50 km.
 Creating the infrastructure for QKD is challenging but it is just the first step. Once transmitted, encription keys must be kept and used. Secure Encryption Key management across all protocol layers will require the integration of QKD with classical cryptography including the actual libraries and procedures impelemented at the diverse layers of the communiction protocols. But this is another story…
Creating the infrastructure for QKD is challenging but it is just the first step. Once transmitted, encription keys must be kept and used. Secure Encryption Key management across all protocol layers will require the integration of QKD with classical cryptography including the actual libraries and procedures impelemented at the diverse layers of the communiction protocols. But this is another story…
CONCLUSION
The first quantum revolution – understanding and applying physical laws of the microscopic realm – resulted in ground-breaking technologies such as the transistor and laser. The second quantum revolution is taking quantum theory to its technological consequences, leading to devices with fundamentally superior performance and capabilities for sensing, measuring, imaging, communication, simulation and computing. Some are starting to be commercially exploited. Others may still require years of careful research and development. Yet others we cannot even imagine today.
To accelerate the maturity of QKD, it is important to focus the attention to identify the practical implementation issues, to investigate the technology readiness for a European digital service infrastructure and to find out where QKD deployment makes sense by the identification of the infrastructures for which the integration of QKD is economically justified with technological and economic performance assessment.
In the meanwhile, to make the vision of a future European quantum-based key distribution network real, Telco equipment manufacturers, users, network operators, QKD equipment providers, digital security professionals and scientists shall work together.
Italtel can support QKD research to reach the level of more practical use, contribute to extend research into a competitive industry with commercial products and be an experienced partner in managing a complex ecosystem.